 Since 2008, the year of the worst financial crisis since the Great Depression of the 1930s, the U.S. Department of Defense has funded a multimillion dollar university research program to probe the complex dynamics of mass social and political movements, anticipate global trends, and ultimately augment the intelligence community’s preparations for civil unrest and insurgencies both abroad and at home.
Since 2008, the year of the worst financial crisis since the Great Depression of the 1930s, the U.S. Department of Defense has funded a multimillion dollar university research program to probe the complex dynamics of mass social and political movements, anticipate global trends, and ultimately augment the intelligence community’s preparations for civil unrest and insurgencies both abroad and at home.
Part of that has involved developing advanced new data mining and analysis tools for the U.S. military intelligence community to pinpoint imminent and potential threats from individuals and groups.
Among its many areas of focus are ongoing projects at Arizona State University (ASU) designed to enhance and automate the algorithms used by intelligence agencies like the NSA to analyze “open source” information from social media in order to track the potential threat-level to U.S. interests. Formal organizations and broad social networks as well as individuals could be identified and closely monitored with such tools to an unprecedented degree of precision.
Loosely defined concepts of political “radicalism,” violence and nonviolence, as well as questionable research methodologies, open the way for widespread suspicion of even peaceful activist groups and their members, and the equation of them with potential terrorists. Civil society organizations in the U.K., including both Muslim religious groups and non-religious anti-war networks, have been prioritized for study to test and improve the effectiveness of these data-mining tools.
Increasingly, though, the automation of threat-detection and terrorism-classification has been accompanied by the automation of killing, in the form of the generation of “kill lists” of terrorism suspects to be targeted via extrajudicial assassination by drone strikes. As President Obama, encouraged by powerful lobbies in the defense industries, has paved the way for the systematic integration of drones into domestic law-enforcement and homeland security operations, the prospect of extrajudicial assassinations occurring on U.S. soil are no longer merely hypothetical.
Now, new but little-known Pentagon directives authorize the use of armed drones against American citizens in the homeland in the context of domestic emergencies.
**
Flawed DoD Algorithms Determine Extrajudicial Assassinations
**
Algorithms of Death
“The algorithms being developed at ASU remind me of the algorithms used as the basis for signature strikes with drones,” said Thomas Drake, a former senior National Security Agency executive who leaked information about the NSA’s data-mining project Trailblazer to the press in 2006.
Drake agreed that the algorithms linked to “LookingGlass,” a new Pentagon-sponsored visual intelligence platform, could in fact be applied to fine-tuning the generation of the CIA’s notorious “kill lists.”
“Having the U.S. government and Department of Defense fund this kind of research at the university level will bias the results by default. This is a fall-out of big data research of this type, using algorithms to detect patterns when the patterns themselves are an effect – and mixing up correlation with causality. Under this flawed approach, many false positives are possible and these results can create an ends of profiling justifying the means of data-mining.”
It is now increasingly recognized that U.S. drone strikes against foreign terrorism targets have systematically killed large numbers of civilians, with a 2012 joint Stanford and New York University report suggesting that as few as 2% of casualties are “high-level” targets – an analysis cohering with counterinsurgency expert David Kilcullen’s 2009 estimate showing a “kill ratio” of 50 civilians to one militant, or, in other words, 98% civilian casualties.
“My colleagues in Special Forces tell me that the men on the front line are furious with the lack of accuracy and integrity at the national level, and no longer trust the targeting data,” said former veteran CIA case officer Robert Steele, who previously served as a Marine Corps infantry officer.
“They have seen for themselves how wrong the system is when they look their man in the eyes. Technical surveillance is the most expensive, least useful, and least accurate form of surveillance. Technology is not a substitute for thinking. We must become deeply and broadly expert at the human factor.”
Drones Come Home
U.S. administration officials including Obama himself have repeatedly refused to confirm whether the alleged legal power to conduct extrajudicial assassinations via drone strikes extends to the U.S. homeland. Last year, prior to becoming CIA director, John Brennan told the Senate Intelligence Committee: “…we do not view our authority to use military force against al-Qaeda and associated forces as being limited to ‘hot’ battlefields like Afghanistan.” He referred to Attorney General Eric Holder’s statement that “neither Congress nor our federal courts has limited the geographic scope of our ability to use force to the current conflict in Afghanistan.”
In February 2012, Obama signed in a law directing the Federal Aviation Administration (FAA) to throw American airspace wide open to drones by as early as September 2015. U.S. Customs and Border Protection (CBP) already deploys Predator drones to spot smugglers and illegal immigrants crossing into U.S. territory, and two dozen U.S. police departments have successfully applied for FAA permits for drones. As National Geographic observes, “all 18,000 law enforcement agencies in the U.S. are potential customers.” By 2020, it is estimated that some 30,000 drones would be active across the U.S. homeland.
Documents obtained under Freedom of Information by the Electronic Frontier Foundation (EFF) show that police plan to use drones essentially for surveillance. In Seattle and Miami, drones are already being used during criminal investigations and in “hot pursuit” of suspects, and could be used during natural disasters along with “specific situations with the direct authorization of the Assistant Chief of the Homeland Security Bureau.” Hundreds of “domestic drone missions” have been flown by CBP on behalf of other state and local agencies.
Last year, government documents revealed that Department of Homeland Security had customized its Predator B drones, built originally for foreign military operations, for domestic surveillance tasks and to “respond to emergency missions across the country,” including “identifying civilians carrying guns and tracking their cell phones.”
These drones are now being used on U.S. soil by the FBI, Secret Service, Texas Rangers and some local police forces. The DHS had also proposed to arm its domestic fleet of border patrol drones with “non-lethal weapons designed to immobilize TOIs [targets of interest]” – an option also being pursued by local police agencies that want to arm drones with rubber bullets, tear gas and other riot control weapons.
According to an unclassified U.S. Air Force document, the deployment of military drones in U.S. airspace will be controlled by the Pentagon and will be able to monitor unidentified groups, as well as “specifically identified” individuals with the Secretary of Defense’s approval. Military drones “are allowed to fly drones in public areas and record information on domestic situations,” noted Jennifer Lynch of the Electronic Frontier Foundation.
Executive Decisions
In February 2013, an extraordinary Pentagon directive authorized the deployment of U.S. military resources and personnel to respond to domestic emergencies, quell civil unrest and support civilian law enforcement in a domestic terrorism incident. The new directive builds on an earlier 2010/2012 DoD directive specifically authorizing the use of military surveillance drones on U.S. soil under Pentagon authority.
Although that directive prohibited the use of “armed” drones for “DSCA [Domestic Support to Civil Authorities] operations,” the new 2013 directive for Domestic Support to Civil Law-Enforcement Agencies goes further. It broadly asserts that “the Secretary of Defense may authorize the use of DoD personnel in support of civilian law enforcement officials during a domestic terrorism incident.”
Unlike the older directive, it stipulates that U.S. military commanders, including those at USNORTHCOM, USPACOM, and USSOCOM, would receive blanket authority over “operations, including the employment of armed Federal military forces at the scene of any domestic terrorist incident.” No limit is specified on what kind of “armed military forces” the Pentagon can conceivably deploy.
The “hypothetical” but nevertheless real extension of powers here was confirmed when Republican Senator Rand Paul asked Attorney General Holder to confirm the Obama administration’s position on conducting armed drone strikes on U.S. soil.
Holder wrote back that “the president could conceivably have no choice but to authorize the military to use such force if necessary to protect the homeland in the circumstances like a catastrophic attack.”
While denying any specific “intention” to do so, Holder conceded “it is possible, I suppose, to imagine an extraordinary circumstance, in which it would be necessary and appropriate under the constitution and applicable laws of the United States for the president to authorize the military to use lethal force within the territory of the United States.”
Although Holder’s comments were widely publicized last year, their pseudo-legal parallel in the form of the Pentagon’s 2013 directive was not. The latter demonstrates that Holder’s consideration of the U.S. military’s legal authority to execute drone strikes on U.S. soil is far from “hypothetical.” On the contrary, the U.S. military was determined to ensure that this extraordinary authority was formally adopted.
I asked the U.S. Department of Defense whether it could confirm that the Minerva-funded data-mining research would not be used to support the U.S. intelligence community’s analytical tools to identify terrorism suspects, in particular to identify targets for extrajudicial assassination. I did not receive a direct answer to this question.
“Research in these areas will improve strategic and operational responses to insurgencies,” said Dr. Erin Fizgerald, chief of the Minerva program. “Perhaps more importantly, these efforts will help analysts faced with a particular political environment that seems ripe for mass mobilization – or a particular movement that appears to be turning violent or destabilizing a government – know where to look to understand a particular movement and its implications for society.”
Global Instability
Prof. Mark Woodward, an anthropologist who leads the ASU projects funded by the DoD’s Minerva Research Initiative, is also affiliated to the CIA-funded Political Instability Task Force (PITF), originally formed in 1994 by appointment of the U.S. government. Although the PITF boasts of developing a predictive model with a “two-year lead time and over 80% accuracy” based purely on modelling “political institutions, and not economic conditions, demography, or geography,” in practice U.S. intelligence was unable to anticipate the unprecedented wave of instability that has swept across the Middle East and North Africa since 2011.
The Pentagon Minerva program addresses this gap in attempting to account for a complex range of interconnected factors beyond political institutions, including the impacts of environmental, energy and economic crises.
As I reported last year, the NSA’s surveillance programs are linked to extensive Pentagon planning for civil unrest in the context of escalating risks from climate, oil, food and economic shocks. Official documents over the last decade confirm that the intelligence community anticipates a heightened threat of instability, including “domestic insurgencies,” due to social and political collapse triggered by such shocks.
As episodes like the recent conflagration in Ferguson demonstrate, the Pentagon’s fears of a future of imminent domestic civil unrest are already being borne out.
Dr. Nafeez Ahmed is a bestselling author, international security scholar, investigative journalist and regular Guardian contributor on the geopolitics of interconnected environmental, energy and economic crises. This article was originally published on Occupy.com and is the fourth and last part of an investigation published. The first part can be read here, the second part here and the third part here.
Photo by Truthout on flickr
 According to CIA Director John Brennan, the War on Terror is now being waged online. In a recent speech at the Council on Foreign Relations, Brennan warned about the threat of cyber terrorism and said the government needs to secure the internet.
According to CIA Director John Brennan, the War on Terror is now being waged online. In a recent speech at the Council on Foreign Relations, Brennan warned about the threat of cyber terrorism and said the government needs to secure the internet.








 [Stasi Museum : Germany. Reprinted with permission from White Fungus]
[Stasi Museum : Germany. Reprinted with permission from White Fungus] 

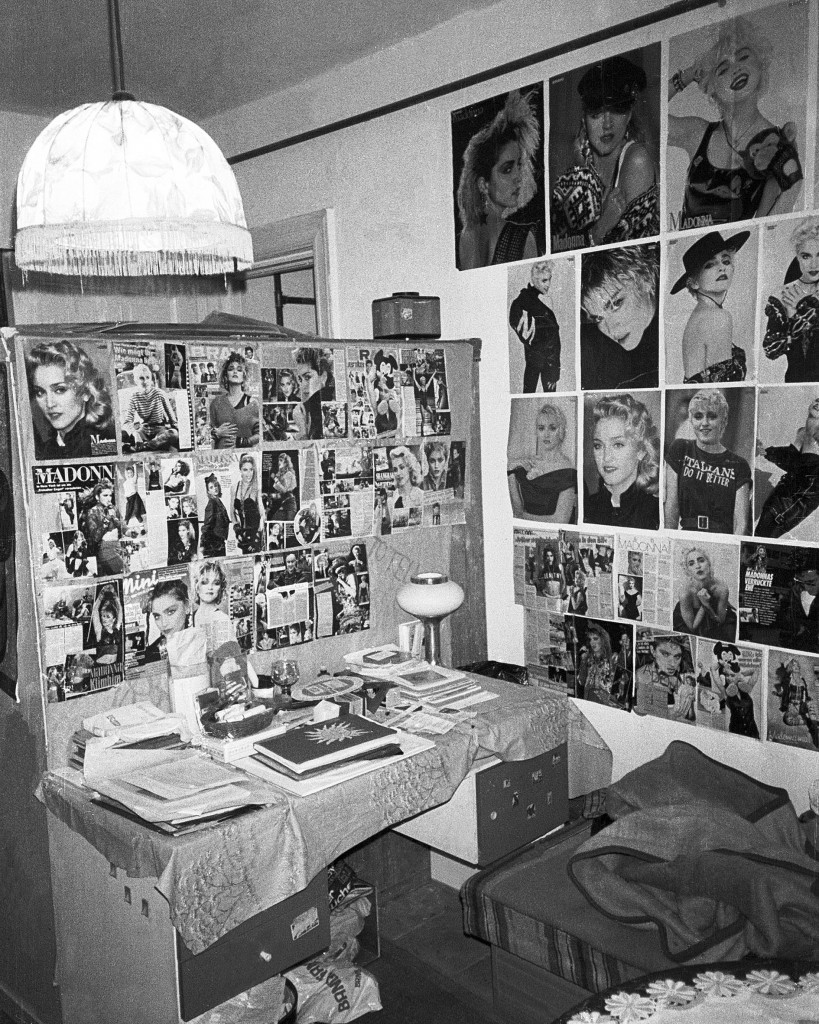 [Surveillance photo of a bedroom of a teen with alleged pro-Western sympathies. Reprinted with permission from White Fungus]
[Surveillance photo of a bedroom of a teen with alleged pro-Western sympathies. Reprinted with permission from White Fungus] Since 2008, the year of the worst financial crisis since the Great Depression of the 1930s, the U.S. Department of Defense has funded a multimillion dollar university
Since 2008, the year of the worst financial crisis since the Great Depression of the 1930s, the U.S. Department of Defense has funded a multimillion dollar university  Joe Rogan defines new media. He’s a comedian, MMA fighter and former Fear Factor host who also pioneered The Joe Rogan Experience (
Joe Rogan defines new media. He’s a comedian, MMA fighter and former Fear Factor host who also pioneered The Joe Rogan Experience (