 MEDIA ROOTS — The drums of war can be heard in the distance as the mainstream media begins to grease the wheels of the war machine. This time Iran finds itself in the crosshairs of Western aggression as Israel is perched ready to strike. The United States military, now firmly in the grasp of the United Nations, will undoubtedly support Israel’s efforts both directly and indirectly. In fact, the collusion between America and Israel against Iran is already deeply entrenched. The use of the Stuxnet computer worm is an excellent example of both the collusion and existence of an already occurring shadow war.
MEDIA ROOTS — The drums of war can be heard in the distance as the mainstream media begins to grease the wheels of the war machine. This time Iran finds itself in the crosshairs of Western aggression as Israel is perched ready to strike. The United States military, now firmly in the grasp of the United Nations, will undoubtedly support Israel’s efforts both directly and indirectly. In fact, the collusion between America and Israel against Iran is already deeply entrenched. The use of the Stuxnet computer worm is an excellent example of both the collusion and existence of an already occurring shadow war.
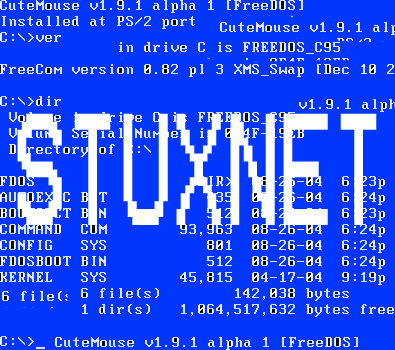
“Cyber warfare against physical infrastructure is absolutely feasible,” said Carey Nachenberg of the Symantec Corporation during a recent lecture at Stanford University. He is referring to the most complicated piece of malicious software (malware) ever built–Stuxnet. More expansive than any other computer virus ever created, the Stuxnet weapon has new techniques of penetration, sleeping and stealth. And it was reported by the Institute for Science and International Security to be responsible for the sudden Iranian replacement of roughly 1,000 uranium enrichment centrifuges at the Natanz nuclear facility.
One must be very careful when considering these “expert” reports, cited by the mainstream media as fact. The founder of the Institute for Science and International Security and co-author of the previously mentioned report, David Albright, has walked both directions on this path before. In 2003, Albright argued that Iraq had reconstituted its nuclear, biological and chemical weapons programs in the lead up to the Iraq war. Conversely, Albright argued that centrifuge tubes found in Iraq were likely not to be for uranium enrichment. To his credit Albright said, “…In this case, I fear that the information was put out there for a short-term political goal, to convince people that Saddam Hussein is close to acquiring nuclear weapons.”
It appears Albright is sensitive to exacerbating intelligence to promote or justify an entrance to war, on the other hand we can see he has some experience perpetuating erroneous intelligence to satiate the war hawk appetite. Nonetheless, we can safely assert that Stuxnet is more non-fiction than the fictional Iraqi weapons of mass destruction. On November 23, 2010, Ali Akbar Salehi, Iranian Foreign Minister confirmed that malware had indeed attacked Iran when he said, “One year and several months ago, Westerners sent a virus to [our] country’s nuclear sites.”
While the mainstream media characterizes the war against Iran as an act yet to occur, it can be said Stuxnet is a weapon of war already deployed alongside the use of targeted assassination. The Stuxnet worm and assassinations of nuclear scientists are indeed Declarations of War that violate Iran’s sovereignty. One can only imagine if this scenario was reversed finding Israel and the United States the subject of equivalent Iranian attacks, it would most definitely be viewed as a Declaration of War.
One cannot begin to understand the reasons behind Western targeting of Iran until you consider Britain’s role. Britain created Israel and dominates the trajectory of American foreign policy. In the dusk of the 19th Century, Iran was subjected to British and Russian aggression known as the “Great Game.” The British invaded again in the 20th Century, thus the Iranians have endured 200+ years of invasion, territorial concessions and castration of regional influence as a result of British and Russian imperialism. The seeds of distrust had been sewn for multiple generations.
In 1951, Prime Minister Dr. Mohammad Mosaddegh nationalized Iran’s petroleum industry. Britain’s Winston Churchill embargoed Iranian oil and enlisted American President Dwight D. Eisenhower to carry out Operation Ajax. This was the first time the United States had openly overthrown a democratically elected civilian government. The roots of distrust were now firmly taking hold as Uncle Sam lined up to slide down the slippery slope of imperialism. Indeed the clouds of war cast shades of history repeating itself.
Grand Ayatollah Sayyed Ruhollah Musavi Khomeini an expert in Islamic Law and jurisprudence, philosopher, poet, and Sufi mystic returned from 16 years of exile in 1979, to steamroll the provisional government and appoint his own interim government. Iran has been in control of its own destiny since this revolution and this has infuriated Western powers, especially Britain. In November of 2011, the British embassy in Tehran was stormed on the heels of an International Atomic Energy Agency report. The British-Iranian relationship is at a new low. Britain certainly has and will have a hand in assisting Israeli and/or American aggression, since it is the wizard behind the curtain.
The United States made it possible for India to acquire nuclear weapons, opaquely provided Israel with nuclear weapons, clumsily allowed Pakistan to acquire nuclear weapons, occupies countries on both the eastern and western borders of Iran and is quite likely the origin of at least pieces of Stuxnet. Iran is infinitely patient to endure centuries of imperialism and these modern Declarations of War. American citizens can only hope these years of diplomacy at the gates of war have provided Iran with the diplomatic savvy to negotiate an aversion to war. America cannot afford the blood and soul of one more American soldier in the interests of British and Israeli imperialism. Iran is sovereign and this sovereignty should be respected, engaged and the resulting goodwill harvested.
Chris Martin for Media Roots
***
History of US Intervention in Iran since 1953
***
Photo by Robbie Martin for Media Roots









 MEDIA ROOTS — During an episode of
MEDIA ROOTS — During an episode of  MEDIA ROOTS – You often hear the term Gulag and think of a secret prison in a third world dictatorship, where its purpose is to break you down, humiliate and torture you. This style of imprisonment has been frequently used by members of the US military in Afghanistan, Gitmo and Iraq.
MEDIA ROOTS – You often hear the term Gulag and think of a secret prison in a third world dictatorship, where its purpose is to break you down, humiliate and torture you. This style of imprisonment has been frequently used by members of the US military in Afghanistan, Gitmo and Iraq.  MEDIA ROOTS – The feverish hysteria of the “red scare” during the 1950s and 1960s prompted the Central Intelligence Agency to do some dirty deeds, not the least of which was a pet project called Operation Midnight Climax. The C.I.A. conducted the operation in the hopes of finding a truth serum by dosing civilians with psychotropic drugs, namely lysergic acid diethylamide. Subsumed by the mind control program
MEDIA ROOTS – The feverish hysteria of the “red scare” during the 1950s and 1960s prompted the Central Intelligence Agency to do some dirty deeds, not the least of which was a pet project called Operation Midnight Climax. The C.I.A. conducted the operation in the hopes of finding a truth serum by dosing civilians with psychotropic drugs, namely lysergic acid diethylamide. Subsumed by the mind control program  MEDIA ROOTS — The U.S.
Government’s raging paranoia regarding terrorism has now led to a high-octane
obsession with perpetual and complete surveillance of its citizens in every
manner
MEDIA ROOTS — The U.S.
Government’s raging paranoia regarding terrorism has now led to a high-octane
obsession with perpetual and complete surveillance of its citizens in every
manner 